The Sonatype Security Research team is currently tracking an ongoing campaign on the npm registry that uses npm packages to retrieve and exfiltrate your Kubernetes configuration and SSH keys to an external server.
Our automated malware detection systems have identified at least 14 such packages thus far. We have been reporting these packages to the npm registry admins as these surface, following our analysis.
These packages, analyzed by Sonatype security researchers Carlos Fernandez and Gustavo Simoes, attempt to impersonate JavaScript libraries and components, such as ESLint plugins and TypeScript SDK tools. But, upon installation, multiple versions of the packages were seen running obfuscated code to collect and siphon sensitive files from the target machine.
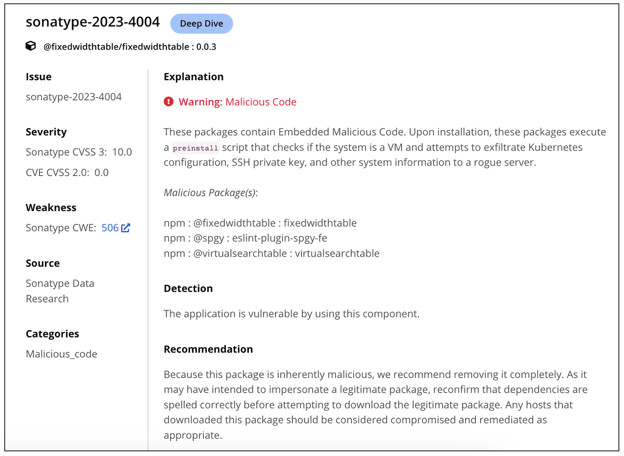
Tracked as Sonatype-2023-4000 and Sonatype-2023-4004, these packages are:
@am-fe/hooks
@am-fe/provider
@am-fe/request
@am-fe/utils
@am-fe/watermark
@am-fe/watermark-core
@dynamic-form-components/mui
@dynamic-form-components/shineout
@expue/app
@fixedwidthtable/fixedwidthtable
@soc-fe/use
@spgy/eslint-plugin-spgy-fe
@virtualsearchtable/virtualsearchtable
shineouts
Published in batches from different npm accounts, each of these packages scored no more than 200 downloads. A common factor linking these accounts was the use of the domain `app.threatest.com` within each of these malicious packages.
Let's take @fixedwidthtable/fixedwidthtable as an example:
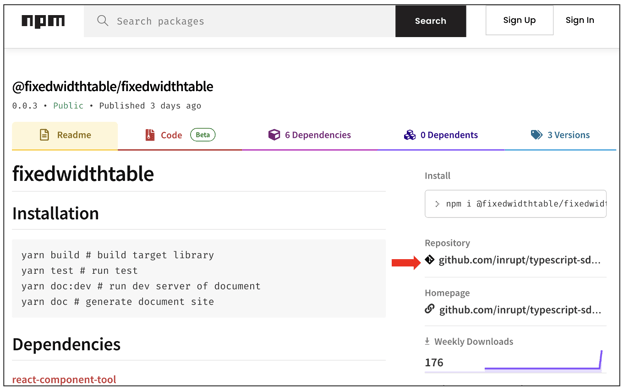
First anomaly, Simoes pointed out, was that the package calls itself "fixedwidthtable," but its npm page links to a "typescript-sdk-tools" GitHub repository – which is not descriptive of the component.
Secondly, the versions of the package do contain functional code and scripts borrowed from genuine open source packages, with some differences.
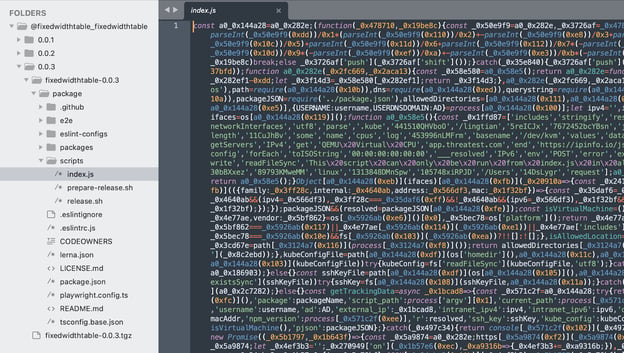
"The structure of the code looks like typescript-sdk-tools but the files are different," says Simoes.
Specifically, under the scripts folder, we notice an "index.js" file that runs obfuscated code:
Other packages identified as a part of the campaign contained identical code and employed similar tactics of impersonating legitimate open source libraries.
We spent some time deobfuscating and understanding the payload in these packages.
Fernandez further pointed out that earlier versions of some packages, e.g. "@am-fe/hooks," contained a plaintext (unobfuscated) version of the attack payload, which helped us confirm what the attacker's intentions were.
"The @am-fe/hooks package contains a non-obfuscated and an obfuscated version," states Fernandez. "These exfiltrate the Kubernetes config, SSH keys, and other sensitive bits of information."
This can be clearly observed in the @am-fe/hooks version 0.0.1-beta.3 below:

Along with SSH keys and Kubernetes config, the script collects a system's basic fingerprinting information, such as username, IP address, hostname – a trend we have seen in basic PoC exploits before. However, covert collection of these additional sensitive files with no warning whatsoever, combined with the deceptive metadata published to the npm registry for these packages should raise alarms and is a clear sign of malicious intent.
Fernandez also stressed that unauthorized access gained by the threat actor to a Kubernetes cluster could become problematic if they were to additionally exploit recently disclosed vulnerabilities against the cluster.
At the time of writing, the domain app.threatest[.]com being used by these packages was seen resolving to two Cloudflare IP addresses, 172.67.141.49, and 104.21.9.30, making it hard to attribute to a particular entity or known threat actors. The use of Mandarin in comments (i.e. "// 获取客户端外网 IP 地址" in line 49, which means "Get the client's external IP address") is also interesting but again, without additional insight, is by no means indicative of a specific threat actor.
We attempted to reach out multiple times to the purported publishers of these packages as well, both using the information present in the package metadata and the domain's WHOIS records, but did not hear back.
For all intents and purposes, based on the observations made so far, we are continuing to treat the packages in this campaign as malicious.
Sonatype's products such as Sonatype Firewall and Sonatype Lifecycle stay on top of nascent attacks and vulnerabilities and provide you with detailed insights to thwart Potentially Unwanted Applications (PUAs), malware, and vulnerable components from reaching your builds:
Users of Sonatype Firewall can rest easy knowing that whether or not these types of packages are just a PoC or actually malicious, they would automatically be blocked from reaching their development builds. Either way, you don't want them in your software development life cycle (SDLC).

Ax is a security researcher, malware analyst and journalist with a penchant for open source software. His works and expert analyses have frequently been featured by leading media outlets including the BBC. Ax's expertise lies in security vulnerability research, reverse engineering, and cybercrime investigations. He has a passion for educating a wide range of audiences through writing and vlogs.
Explore All Posts by Ax SharmaTags
